Passwords are one of the most important parts of keeping any account secure, and if you were to gain access to these accounts, you’d have access to personal data, subscriptions, money, and even the victim’s identity. Today, we want to show you just how easy it is to steal a password and gain access to an account.
Directive Blogs
Did you know that tomorrow is World Password Day, 2023? As the result of a campaign to spread awareness of the importance of sufficiently secure passwords, it has become an annual reminder of how critical sufficient passwords are to proper cybersecurity…despite passwords not being sufficient protection on their own. In light of tomorrow’s observance, let’s take some time to review why passwords are important to get right, and what else you need to have in place.
One of the reasons that information technology keeps changing is for the sake of the user and their convenience using it. However, if this convenience comes at the sacrifice of your business’ cybersecurity, it just isn’t worth it. This is the crux of why we always recommend that any organization seeking to use password management should invest in a reputable password management software, rather than the built-in capabilities of modern browsers.
Multi-factor authentication is great when it works, but when it doesn’t, it can leave you in a pretty difficult situation. After all, what happens when all of a sudden, you cannot access your secondary authentication methods? We’re here to help you bypass this particularly challenging and frustrating scenario.
Whether you love them or hate them, passwords serve an important purpose in the realm of cybersecurity. They are the first line of defense against potential threats, yet they are also notoriously easy to crack. Some of the biggest names in technology have been working on ways to get around the challenges presented by password security, including one that we are excited to highlight in today’s blog.
Simple passwords are just not an effective security practice, so if you’re still using credentials like Password, 123456, Guest, or Qwerty, listen up. You need better password hygiene practices before you suffer from a data breach. Here are some ways you can make a better password to protect your business from threats.
Nobody wants to spend their weekend doing paperwork. Nobody wants to spend several evenings in a row sitting over a laptop and slowly digging through every online account they have, resetting every password and carefully documenting everything in a secure password manager. I know this better than anyone, because I forced myself to do it.
Here’s the thing though, EVERYBODY should do it. As soon as possible.
Simple passwords are often the bane of a business’ existence. If you routinely use strings like Password, 123456, Guest, or Qwerty to secure an account, then you need to reexamine your password practices before they lead to a data breach. A good password can go a long way toward helping you in this effort.
User authentication is a critical security feature for a business, specifically because it helps to minimize a significant threat to your business. This is why we’re so adamant that you should require multi-factor authentication wherever it is available… but is a better way to authenticate your users on the horizon?
Passwords are just one part of a comprehensive security strategy, but they are a crucial one. You must make sure that you are investing adequate time and effort into making sure your passwords are secure. This is easier said than done, but by the end of today’s short blog article, you’ll have all the information you need to craft excellent passwords for your accounts.
We talk a lot about preventing threats from seeping into your company, and hoo boy, there are a lot of them. From ransomware to zero-day exploits to targeted social media attacks, there are a lot of threats out there that business owners need to be aware of. We’re not going to talk about any of those today.
Why? Because you, as the business owner, are likely a threat to your own business.
With many businesses’ increased reliance on their information systems and other IT, they need to do everything they can to keep those systems up and running and secure. This not only includes rolling out security systems that support that goal, it also demands they take the action necessary to keep these systems secure. Let’s look at four things you need to do to keep your business’ IT as secure as possible.
Passwords have been a primary data security measure since 1960, when MIT researcher Fernando Corbató suggested the practice—although even he is reportedly slow to take full credit. Why? Well, if you ask Corbató (and his contemporaries, who were the first to implement passwords as we’d recognize them today), the security concerns were limited.
So, have we reached the point where it would be best to replace passwords as the default authentication measure?
Businesses sure use a lot of online accounts, and if they don’t keep track of the passwords associated with these accounts, things can get messy fast. To help with this effort, password managers, or applications that store passwords in an encrypted vault, have really taken off. Here are some of the reasons why businesses invest in password management solutions.
Two-factor authentication is commonplace in the office environment, but it’s not commonplace enough, if you ask us. Too many organizations pass on it, placing their security at risk for no good reason. While the methods might vary, the benefits of two-factor authentication are too good to ignore. We’ll walk you through how to set up two-factor authentication for three of the most common accounts in the business environment: Microsoft, Google, and Apple.
Most accounts these days require a password of some sort, and as such, the average user has countless of these codes that need to be kept both secure and top-of-mind. Some web browsers have built-in password management tools to help make them more user-friendly, but with so much convenience involved, one has to ask whether or not these built-in management tools are as secure as they should be.
It’s true that if they are created to be secure, passwords are hard to remember. There is also no denying, however, how important it is to use different ones for each account, all sufficiently complex. If you are doing things right, you probably have too many passwords to remember, which is why a password management system is a solid tool. This month, let’s take a look at the password management system.
I’m not sure we need to tell you how important passwords are: they are the front-line defense to most of the accounts you create. What is often overlooked is the strategy of how to use a password to successfully protect accounts and data. Today, we will discuss best practices when creating and managing your passwords and how you are likely approaching your password strategy improperly.
Your business’ security largely depends on how secure the passwords are that keep your resources from being accessed without authorization. Despite this, many users—perhaps even you—frequently sacrifice sufficient security measures in favor of the simple and convenient route, cutting corners when coming up with their passwords. Let’s try and remedy this by reviewing a few practices that can help make a password more effective.
The new year is upon us and after the debacle that 2020 was, it is extremely welcome. If you are like us, you have a new set of goals that you’ve created for yourself and are probably looking to improve your professional and personal well-being. One way to do that is to ensure that your accounts are secure. Today, we will be going through how to update your password with Microsoft.
Going through your passwords and updating them every so often is a very wise habit to get into, particularly when they are used to protect a lot of data—as the password to your Google account often is. Considering this, let’s go over how to update your Google password and otherwise lock down your account.
If I were to tell you that one variable was responsible for more than 80 percent of cyberattacks, what would you guess that variable was? If you guessed “stolen access credentials,” you’d be correct. The traditional username/password combination may soon be a thing of the past as more tech companies transition to alternative authentication measures.
The password is the core element of both data security and user authentication. This makes the construction of them extremely important to protecting digital assets. Unfortunately, not everyone understands how to construct passwords that actually work to protect the information on the other side. Today, we will discuss how to build a solid password that works to keep your digital resources safe.
Protecting your online accounts, your data, and your customers’ information is now more important than ever. Industry and state-mandated compliances are now forcing businesses to tighten their cybersecurity, and it’s critical that every human being on the Internet take their own personal security seriously. This guide is designed to provide the best practices for strong passwords.
Your cybersecurity is only as strong as your weakest link, and in many cases, that starts with your passwords. As the Internet of Things continues to become more ubiquitous in our homes and businesses, we risk exposing our private lives to the public-at-large. When we don’t manage our ‘always connected’ devices, we may be placing the security of our businesses and homes at risk.
Passwords… can be annoying, if we’re being honest. They are, however, also incredibly important to your business’ overall security strategy. We’ve all heard the suggestions on how to create secure passwords. As it turns out, there is more to modern security then that. Let’s explore a few options to help you create useful passwords, and take a look why passwords are only the beginning.
 This holiday season might leave technology and entertainment supergiant Sony with nothing but a big lump of coal in its stocking. In a high-profile hack, hackers continue to leak Sony’s employees’ sensitive information like Social Security numbers, passports, and even personal emails. This is obviously an issue for the company, but so is its lack of IT security, as shown by their passwords being stored in a folder named “Passwords.”
This holiday season might leave technology and entertainment supergiant Sony with nothing but a big lump of coal in its stocking. In a high-profile hack, hackers continue to leak Sony’s employees’ sensitive information like Social Security numbers, passports, and even personal emails. This is obviously an issue for the company, but so is its lack of IT security, as shown by their passwords being stored in a folder named “Passwords.”
Password security is a tricky part of running a business. After all, it’s not just dealing with your own password, but those of the many employees all throughout your organization. In times like this, it’s helpful to provide them with a list of how to make the best passwords possible. Here are a couple of examples for what to do, as well as what you shouldn’t do, when building a proper password.
Passwords are always a major pain point for businesses, but in some industries, their importance is emphasized more than others. In particular, government-based organizations need to be prepared to keep more secure passwords. While we understand that not all organizations are government-based, there’s something to be said about proper password practices that we can all learn something from.
Passwords are all over the place these days, whether they’re required to access an online account, or access the devices used to open these accounts. While both types of passwords can make for ideal security conditions, this is only the case if the passwords are strong. If your passwords can be guessed by just about anyone, can you really call it a security measure? New insights from SplashData show that passwords aren’t being considered as much as they need to be.
There is no understating the importance of strong, reliable passwords to your organization’s network security, especially to protect its wireless connection. However, this can create some friction with your staff when they try to connect to Wi-Fi using their mobile device. To make accessing the Internet easier, scannable QR codes can be used to connect to the Internet.
This has been a pretty common topic for us on the Directive blog. We've seen a lot of Upstate New York clients and customers suffer the consequences when online retailers and other account providers experience a security breach. It is equally vital for consumers to know what to do in the event of a security breach as it is the company that is actually breached.
Your identity has quite a lot of value, especially in the wrong hands. Security firm ZoneAlarm put together some numbers in 2011 concerning identity fraud, and it even shocked us. Let's talk about a few of these statistics and what it means.
 For sites you need to log into often, having your browser remember your password can save you time logging in, especially if you are using secure passwords that you might need to look up otherwise. There are circumstances where you might want to manage what personal information gets stored in your web browser.
For sites you need to log into often, having your browser remember your password can save you time logging in, especially if you are using secure passwords that you might need to look up otherwise. There are circumstances where you might want to manage what personal information gets stored in your web browser.
On the topic of identity theft, social media accounts are becoming a high target for hackers, especially for spreading malicious viruses. To some, losing control over their Facebook or Twitter accounts could be just as devastating as having their credit card stolen. Trouble is, for many users, having one login account stolen means hackers have access to their other accounts too.
With every successful intrusion and theft of data, the images of hackers as criminal masterminds and unstoppable forces of technology gone awry grow. In fact, there’s an increasing narrative that hackers are everywhere, just waiting to use their mad ‘skillz’ to steal your credit card information and buy their limited edition dolls, sorry, “action figures.” Worse, they’re just waiting to hold your data hostage and extort ransom from your business.
 Security is a hot-button issue for all types of businesses, but cyber security is such a complex subject that it’s difficult to jam-pack its many intricacies into one blog article. Sometimes understanding just a few ways to improve your business’s security practices can be a significant benefit for your organization.
Security is a hot-button issue for all types of businesses, but cyber security is such a complex subject that it’s difficult to jam-pack its many intricacies into one blog article. Sometimes understanding just a few ways to improve your business’s security practices can be a significant benefit for your organization.
 Changing your password is a pain. After you’ve gone several months with the same one, it can be difficult to remember your new password. Despite this, it’s always recommended that you change your passwords often. Unfortunately, when you change all of your passwords often, it’s even easier to forget them. Instead of using a post-it note on your monitor, you should instead try using a password manager.
Changing your password is a pain. After you’ve gone several months with the same one, it can be difficult to remember your new password. Despite this, it’s always recommended that you change your passwords often. Unfortunately, when you change all of your passwords often, it’s even easier to forget them. Instead of using a post-it note on your monitor, you should instead try using a password manager.
 We see a lot of password-bashing these days, and some people have lost faith in them as a security measure. But, unfortunately, a lot of the blame for this lies in human memory. We just don’t pick passwords that are strong enough. In fact, a mind-numbing one in 20 people still use “password” to keep their information safe.
We see a lot of password-bashing these days, and some people have lost faith in them as a security measure. But, unfortunately, a lot of the blame for this lies in human memory. We just don’t pick passwords that are strong enough. In fact, a mind-numbing one in 20 people still use “password” to keep their information safe.
 Last week, the Heartbleed bug was identified as a weakness in the OpenSSL cryptographic library, potentially leaking two-thirds of the Internet's secure information from any websites utilizing this encryption style. While most major websites such as Google, Yahoo, and Facebook released patches quickly, it does little to actually remediate the problem. Your data could have been leaked over the year-plus that the vulnerability could have been accessed. There is no way to know if it has been compromised.
Last week, the Heartbleed bug was identified as a weakness in the OpenSSL cryptographic library, potentially leaking two-thirds of the Internet's secure information from any websites utilizing this encryption style. While most major websites such as Google, Yahoo, and Facebook released patches quickly, it does little to actually remediate the problem. Your data could have been leaked over the year-plus that the vulnerability could have been accessed. There is no way to know if it has been compromised.
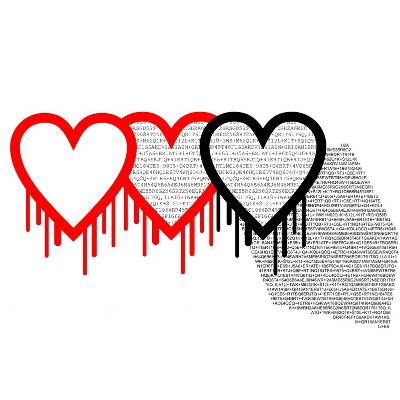 On April 7th, a new bug on the Internet was discovered that's putting millions of users' personal data at risk. Given the name "Heartbleed bug," it's capable of allowing infiltrators to collect information while you are securely browsing a SSL/TLS website. Since SSL/TLS is so widely used, it's very probably that your personal data is at risk.
On April 7th, a new bug on the Internet was discovered that's putting millions of users' personal data at risk. Given the name "Heartbleed bug," it's capable of allowing infiltrators to collect information while you are securely browsing a SSL/TLS website. Since SSL/TLS is so widely used, it's very probably that your personal data is at risk.
 On December 3, 2013, security company Trustwave discovered over two million stolen user passwords for popular online services like Facebook, LinkedIn, Google, Twitter, Yahoo, and 93,000 other websites. There's a high probability that you use one of the services affected by the hack. Is your personal information compromised?
On December 3, 2013, security company Trustwave discovered over two million stolen user passwords for popular online services like Facebook, LinkedIn, Google, Twitter, Yahoo, and 93,000 other websites. There's a high probability that you use one of the services affected by the hack. Is your personal information compromised?
Ever since the public has been logging on to the Internet, certain people have been using the Internet to take advantage of others. Whether it be through scams, viruses, malware, phishing, or a whole slew of other dangerous activity, cyber criminals have been very good at making Internet security an industry on its own. With the colossal popularity of social networks like Twitter and Facebook, miscreants are capable of targeting even more users than ever before. On top of that, their methods seem to be hitting people where it hurts. Learn how you can prevent falling into one of their traps.
The problem with carrying around an expensive, portable piece of equipment is that it's possible for someone to pick it up and run with it. According to LoJack, a security firm that focuses on stolen property, two million laptops are stolen each year. What should you do if you are a victim of laptop theft?
 Technology is supposed to make things easier, yet it’s a common source of frustration when it doesn’t do what it’s supposed to. As an IT company, we experience technology frustrations all the time, and we wish that many of these frustrations could just be eliminated altogether. In our opinion, here are four technology frustrations that need to go.
Technology is supposed to make things easier, yet it’s a common source of frustration when it doesn’t do what it’s supposed to. As an IT company, we experience technology frustrations all the time, and we wish that many of these frustrations could just be eliminated altogether. In our opinion, here are four technology frustrations that need to go.








