Directive Blogs
Software Patches Take on New Importance After the WannaCry Ransomware Fiasco
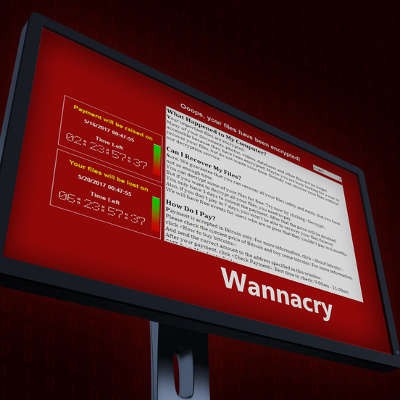
On May 11th, 2017, the world was introduced to the WannaCry ransomware. The ransomware spread around the globe like wildfire, infecting hundreds of thousands of devices and catching many major organizations and businesses by surprise. The full extent of the ransomware’s damage is still being assessed, yet, one thing we do know: this whole fiasco was preventable.
Granted, there’s nothing that any of us could have done to prevent hackers from using a leaked NSA cyberspying tool to deliver their ransomware. Companies that took the time to apply the latest security patches issued by Microsoft back in March were generally spared having their files encrypted against their will. Meanwhile, companies and PC users alike that put off applying the updates were the ones that got slammed.
This incident highlights the importance of applying security patches in a timely manner, as well as poses the question, “Why were there so many organizations that put off applying such a critical patch?” Compared to the average PC user that simply has their system set to automatically install Windows updates as soon as they’re released, enterprises tend to take a different approach.
When it comes to business computing, it’s best practice to first test a new patch before applying it to the company network. A major reason for this is because one can’t be certain of how applying a patch will affect other software until testing first takes place. Worst-case scenario, a patch is applied to a company network that unexpectedly interferes with a mission-critical application. When this happens, productivity is hindered and operations may even grind to a halt.
Considering the potential fallout from this outcome, you can see why a lot of IT departments choose to delay applying newly issued patches. After all, should a patch that’s been applied end up disabling important systems, then going back and undoing the damage just makes the problem worse, and much more expensive.
All that said, organizations hit with the WannaCry ransomware had adequate time for their IT departments to test the security patches issued by Microsoft (in March), before the ransomware began infiltrating systems around the world (in May). Now, we understand that every business has different priorities, and those priorities are reflected by how IT resources get allocated. As an IT company ourselves, we get that and therefore don’t wish to criticize organizations that didn’t apply the security patches soon enough. Instead, we offer our condolences to any business hit with the WannaCry ransomware, and we’re standing by to help resolve any related IT issues.
At the very least, we hope this ransomware attack serves as a wake-up call for organizations of all shapes and sizes when it comes to following through with routine IT maintenance, especially the likes of promptly applying security patches (a top priority, obviously) and properly managing your backups. If you don’t have time for this or find yourself routinely pushing IT responsibilities like testing/applying patches off to the side, Directive can help.
With our managed IT services, you can outsource routine IT tasks to our trained technicians, which can often be handled remotely. They will make sure these tasks are taken care of promptly and efficiently, meaning you “won’t cry” should another ransomware attack make the rounds. To get started today with managed IT from Directive, call us at 607-433-2200.


Comments