With information technology touching nearly every part of modern culture, it isn’t a surprise that it is being utilized by sectors of industry where you may not expect. One of those sectors that may not register as one of the most IT-centric is the criminal justice system. This is largely because it is traditionally thought to be filled with jobs that seemingly haven’t changed much in centuries. Today, we’ll take a look at the technology that fuels today’s criminal justice system and see how municipalities and companies, alike, are benefiting from technology solutions.
Police
To start the journey through the legal system, we’ll start with the people whose job is defined by exercising moral authority: the police. The first thing that anyone needs to know about their investment in IT and their use of technology systems is that, since the police gets a majority of their funding from public money, IT budgets aren’t always in line with a private business’. In fact, some police departments don’t see the point in more IT when good cops are being laid off so they will deliberately cut their IT budgets in line with the budget they get from their municipality.
While IT isn’t always a priority for the police, it can be effective at providing exceptional departmental productivity gains. With the remote nature of the job, most police cars today are outfitted with laptops and Internet accessibility. This allows officers to access motor vehicle and individual information stored on useful databases, but since these machines are hardwired into a car dock, they only get a partial benefit of mobility. Innovative solutions are now being used where police are outfitted with department-owned smartphones and tablets so that officers can access relevant information from outside of their cars.
There are several parts of the job where police can benefit from new technology. Along with the in-car computer networking, and potentially mobile device networking, IT can compliment a lot of what a police officer does. The right IT solution can boost communication, augment (or completely run) operational capabilities, and effectively reduce costs by providing information faster and speeding up procedure. After all, a large percentage of effective policing has to do with having actionable information. As a result, by implementing IT solutions, the public welfare improves--which is the situation that any citizen can ask from their officers of the peace.
From a software perspective, here are three types the typical police department can’t do without:
- Computer Aided Dispatch (CAD) - An application that assists dispatchers route police resources to places of priority need.
- Geographic Information System (GIS) - An application that provides in-depth geographic information to provide dispatchers and officers a comprehensive view of the landscape.
- Records Management System (RMS) - An application that provides officers with access to reliable information to assist them in their duties.
Lawyers
Moving on to the lawyers, we’ll find a professional that is torn between the past and the future. Many lawyers understand that IT can benefit them, but at the same time the simply don’t have time to monkey with technology that, for some, can do more harm than good. The average lawyer that works criminal cases, whether they are prosecutors, defense attorneys, or specialists, understands how to effectively utilize certain technologies to provide their clients the best service possible. After all, they deal with a lot of sensitive information, and have a responsibility to protect it.
Some of the technologies that law firms typically utilize come in the form of business-type solutions that enhance their productivity, efficiency, and data redundancy. Others, however, are best utilized by a business like a law practice. Most practices need strong collaborative systems that allow multiple people to share files, the ability to print off documents, and a central database that has access to documents. These requirements make computing solutions in the cloud a perfect fit for the modern law office. Cloud computing can offer these organizations a way to host all their necessary software, while also providing virtual hardware and redundant storage capabilities without having to pay huge upfront costs.
Lawyers typically use the following software:
- Practice Management - An application that is designed to help lawyers and their staff manage the large quantity of work they are inundated with.
- eDiscovery - An application that makes finding, collection, identifying, and sharing relevant information easy.
- Video Conferencing - Lawyers are extraordinarily busy and often don’t have time for face-to-face meetings. Video conferencing helps fill the void by allowing them to meet with clients, colleagues, and staff from anywhere with an Internet connection.
The Court
Since its main purpose is to be a place to hear arguments, the courtroom doesn’t need all the technology that the police and lawyers use to keep things rolling efficiently along. In fact, most of the technology that is utilized in the duration of a criminal trial would be traditionally provided by the prosecution or defense. This simply isn’t so today. The courtroom of the information age is seeing a major shift, and changing the nature of litigation completely.
The biggest change to the modern courtroom is in the availability of data. Since data is now able to be securely broadcast from cloud servers to devices such as laptops and tablets, the notoriously slow court proceedings’ pace has quickened somewhat. Other technologies like wireless Internet connections and charging ports add to the connected courtroom effectiveness.
Along with the technology people bring in to the courtroom, there are major changes in the technology inside the courtroom itself, too. The modern courtroom features video displays--either in the form of a mounted screen and a LCD projector or smaller, individual screens in the jury box--to provide juries a resource to see evidence. Many courtrooms also have individual witness monitors and annotation monitors.
Since the courtroom only has a couple of static employees, software isn’t typically necessary to manage the staff or used for productivity, but some software is available. There are titles for court and case management, e-filing, and audio-visual that are all found in the modern courtroom.
Corrections
The criminal justice system ends with institutional corrections (prisons and jails) and community corrections (probation and parole). Like the other parts of the system, the corrections system has become dependant on the use of technology, especially for communication. Internet-based databases help corrections professionals track and maintain records on offender rehabilitation, while also helping provide an alternative to incarceration for nonviolent offenders. This provides the public significant cost savings, while also providing correction officers the ability to effectively monitor and manage offender probation.
Since budgetary considerations can really put a damper on the amount of acceptable innovation in corrections, the use of standard information technology is extremely important. It is making prisons and jails safer, and community corrections more effective. No better example of this than then the use of asset tracking technology through an automated offender management system.
The automated offender management system allows multiple users to access (and alter) an offender’s record simultaneously.with other users. This real-time information sharing improves efficiency, as the more information that’s available between multiple elements of the criminal justice system (and in this case, the corrections system) the better the entire system moves. Additionally, by providing real-time inmate information to corrections officers, it will reduce security risks.
If the technologically puerile criminal justice system is utilizing technology to improve operations, your business can, too. To see how Directive’s knowledgeable IT consultants can make technology work for your organization, call us today at 607-433-2200.


 In November of 2016, Governor of New York Andrew Cuomo devoted $30 million dollars to a 50-mile-long flight traffic management system to promote the use of unmanned aircraft systems (more commonly known as drones) for Central New York business purposes. This ‘corridor,’ as it is called, will stretch from Griffiss Air Force Base in Rome to Syracuse by sometime in 2018.
In November of 2016, Governor of New York Andrew Cuomo devoted $30 million dollars to a 50-mile-long flight traffic management system to promote the use of unmanned aircraft systems (more commonly known as drones) for Central New York business purposes. This ‘corridor,’ as it is called, will stretch from Griffiss Air Force Base in Rome to Syracuse by sometime in 2018. There are an unfortunate number of cyber threats out there; protecting your company’s network from these threats is paramount. In order to find out how acquainted you are with the malicious programs and attacks that could harm your business, we’ve devised this quick quiz to test your knowledge.
There are an unfortunate number of cyber threats out there; protecting your company’s network from these threats is paramount. In order to find out how acquainted you are with the malicious programs and attacks that could harm your business, we’ve devised this quick quiz to test your knowledge.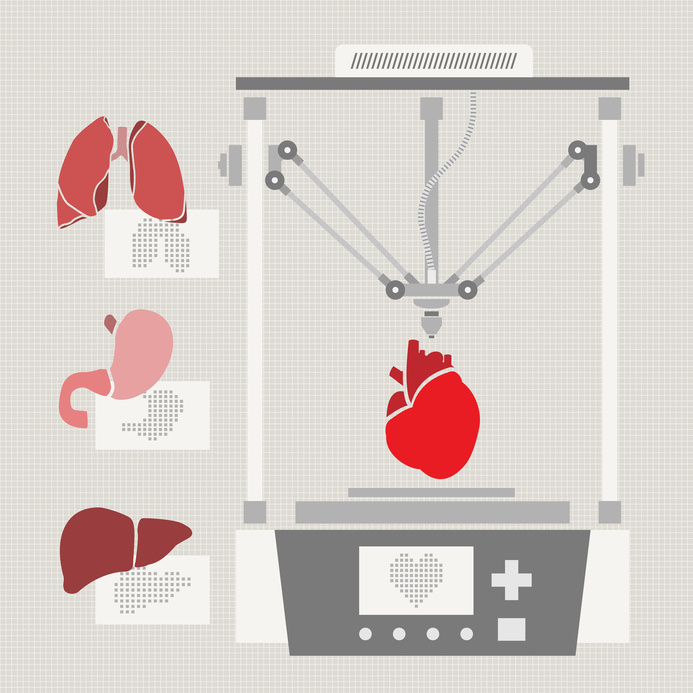 The concept of 3D printing is becoming a factor in more and more industries, perhaps most promisingly in the healthcare sector. This specialization has the potential to revolutionize how patients are treated for some very serious maladies, as well as how well they adjust to their life during the post-treatment stages. However, this application of 3D printing is not without its concerns.
The concept of 3D printing is becoming a factor in more and more industries, perhaps most promisingly in the healthcare sector. This specialization has the potential to revolutionize how patients are treated for some very serious maladies, as well as how well they adjust to their life during the post-treatment stages. However, this application of 3D printing is not without its concerns.